Multi-Factor Authentication Configuration
See background on Multi-Factor Authentication.
In this implementaiton of Multi-Factor Authentication, the user is prompted to authenticate to their upstream identity provider, and, then, a multi-factor challenge is provided via web.
State can be kept in a secure cookie on the ‘auth.DOMAIN’ endpoint. This can allow single-sign-on with multi-factor as well as only requiring a 2nd factor over some time interval.
Supported Methods: WebAuthn (Passkey, USB Authenticator, FIDO U2F, …)
The Web Authentication (WebAuthn) standard is the current best practice. It allows seamless integration of platform-specific features (biometric, TPM) with external U2F and CTAP devices.
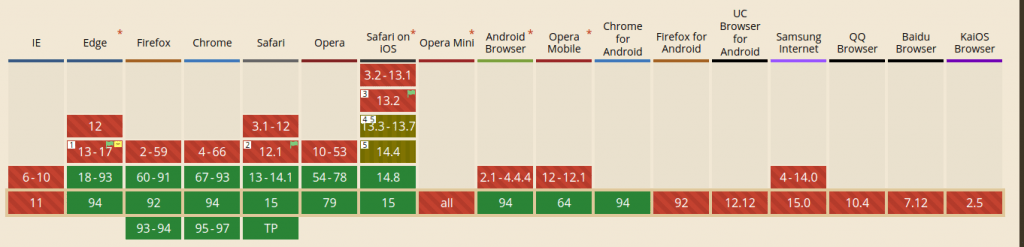
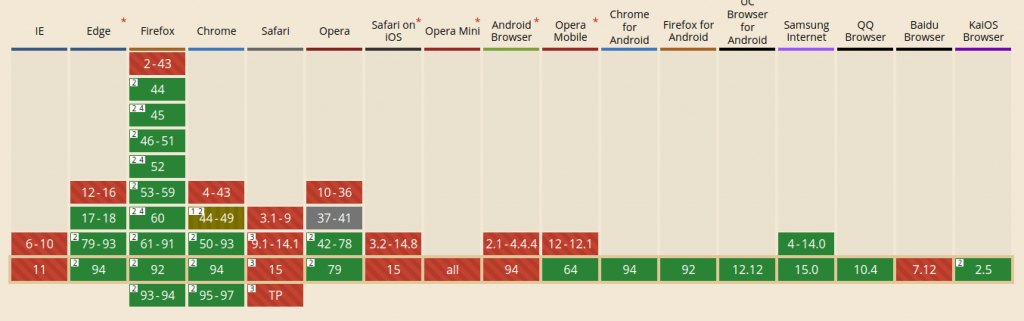
Browsers and versions supporting WebAuthn can be seen here.
WebAuthn is designed to be privacy preserving, no information on the user or device is shared with the network. This includes biometrics.
Supported Methods: TOTP (Time based challenge app)
A time-based one-time password (TOTP) is a universal standard, implemented by many applications (including Authy, Google Authenticator).
TOTP is private (there is no network communication flow) and works even without a graphical or browser flow.
Agilicus’ implementation works with all TOTP-supporting applications, however, we recommend Authy.
Our strategy is to not supply “yet another” TOTP application. Instead, we recommend users use a common one across all websites, including ours.
Web Push
Web Push uses a network authentication profile called VAPID. This is designed to be entirely private: there is no way to identify the user or device receiving the push. In the Web Push model, the user’s browser (whether open or not) will receive a ‘push’ “WAS THIS YOU” message when you try to login, even on another device.
Web Push is secure and convenient. However, the major downside is Apple, which does not support push methods. There is a petition requesting support.
Authentication Rules
Authentication Rules are a type of Conditional Access. They are logically part of the authentication flow, after he user has proven identity. These rules can augment the logic with things like:
Default
Permissive
Strict
Trust On First Use
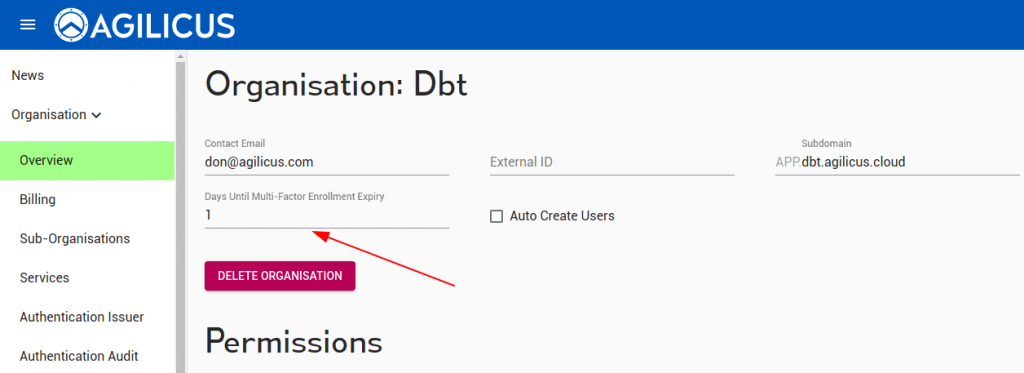
The deadline is set organisation wide, and is the delta from when the user is created until when they must have successfully demonstrated a 2nd-factor setup.
End-User Setup (Profile)
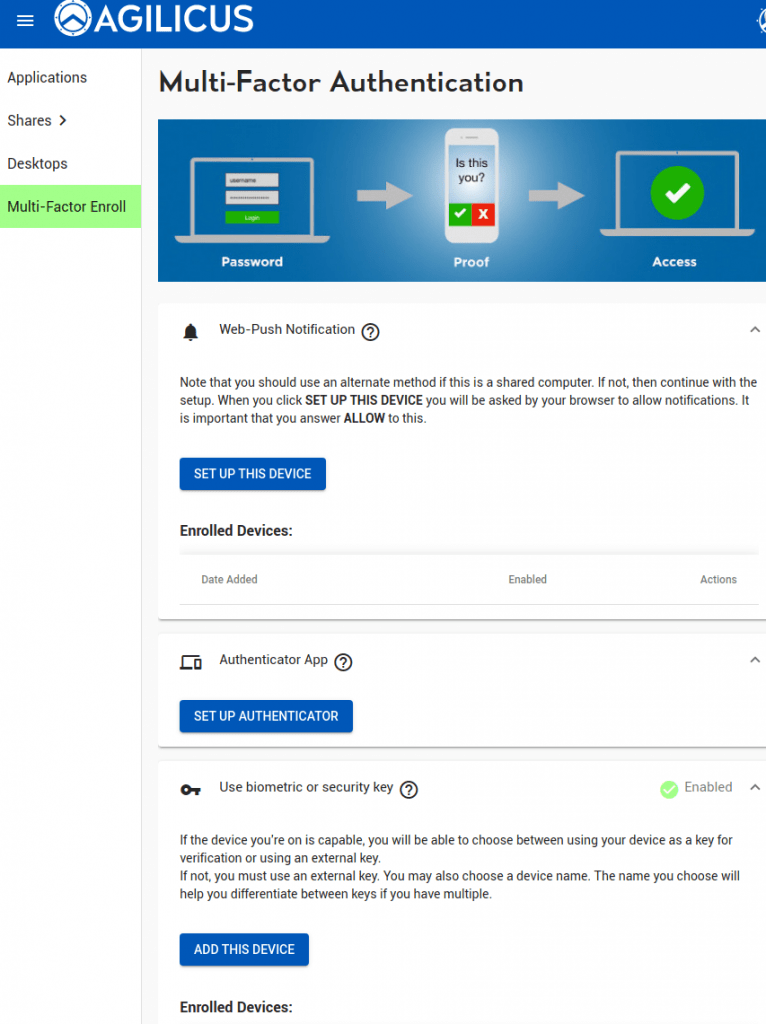
The end user may manually navigate to “Profile” (via https://profile.DOMAIN). They may also install it as a Progressive Web App (PWA), making it appear as a mobile-native application.
In the Profile, the user may setup whichever multi-factor methods their organisation has chosen to support.
if trust on first use is used. the user will be forced here on their first login within the enrolment period.
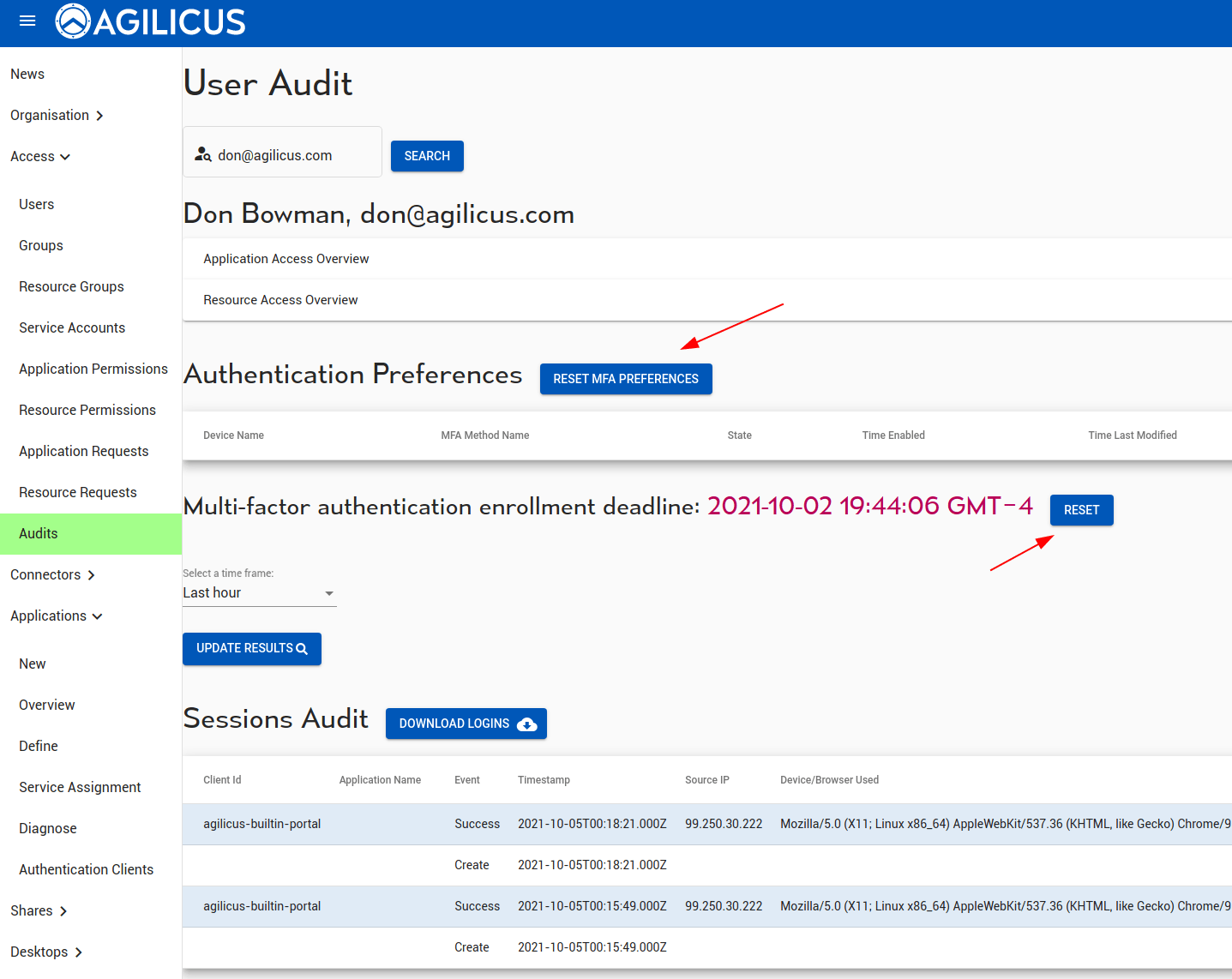
Diagnostics and User Audit
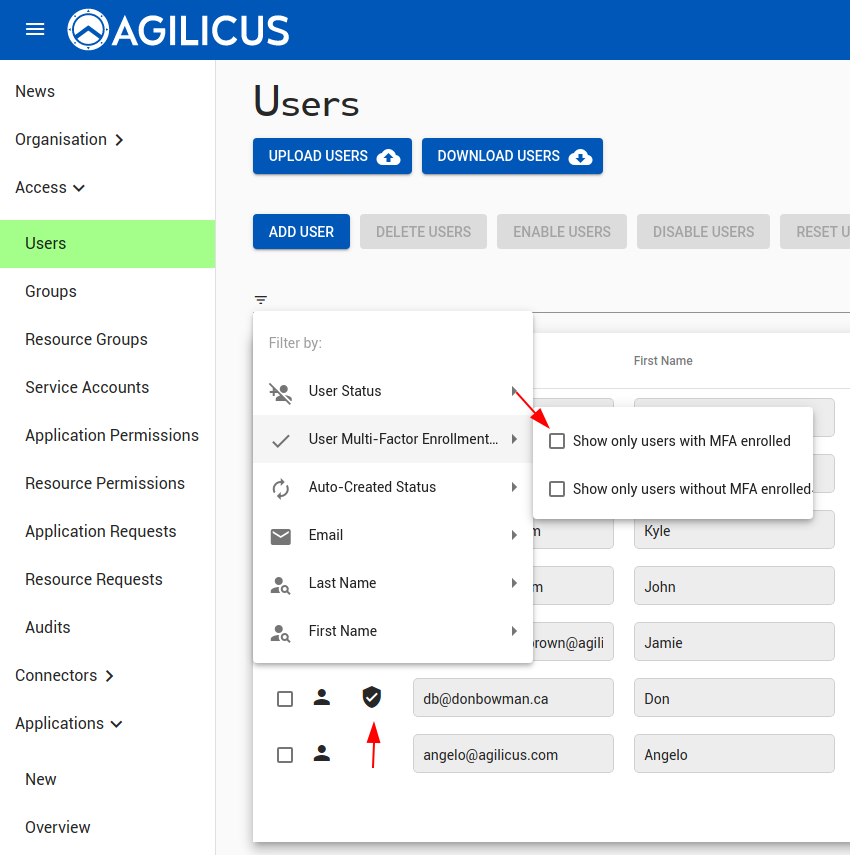
We can see which users have multi-factor setup in the ‘Users’ screen (via the shield). We can also filter to show only user with/without multi-factor authentication enabled.
The “RESET” users option will unset the multi-factor setup & preferences of a user.
We can see the multi-factor sessions and preferences (as well as all other audit information) of a given user on the audits screen. Here too we can reset the trust-on-first-use timeline.
Requiring multi-factor authentication
Normally, a user must periodically present their second factor when authenticating only if they have it enabled. That said, you can configure the policy to require a set of users to have a second factor method configured. If such a user tries to log in when they do have not have a second factor method configured, they will either be asked to enrol one, if they are within the enrolment deadline, or they will be denied access.
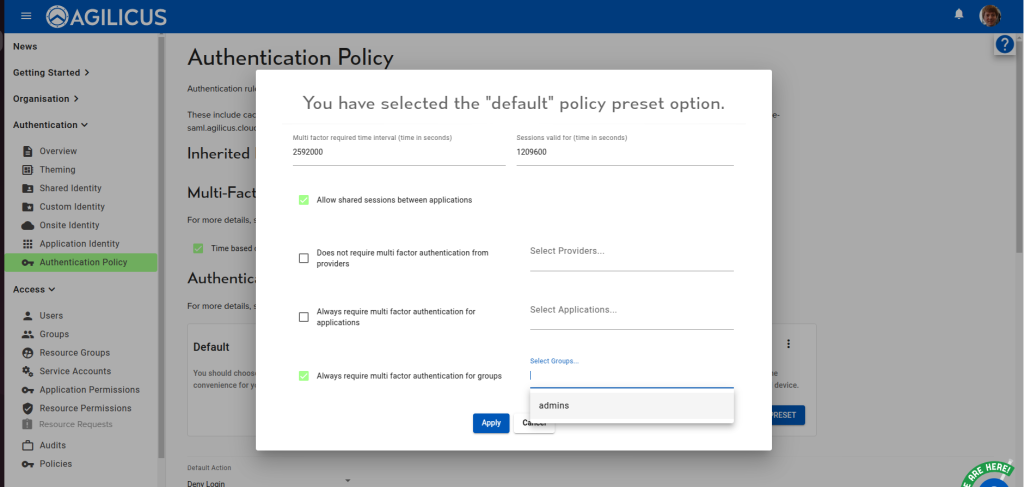
You can configure this setting in one of two ways. If you have not yet customised your authentication policy, you can apply one of the presets. Choose the preset to apply, then select the groups for which you want to force multi-factor authentication in the “Always require multi factor authentication for groups” section.
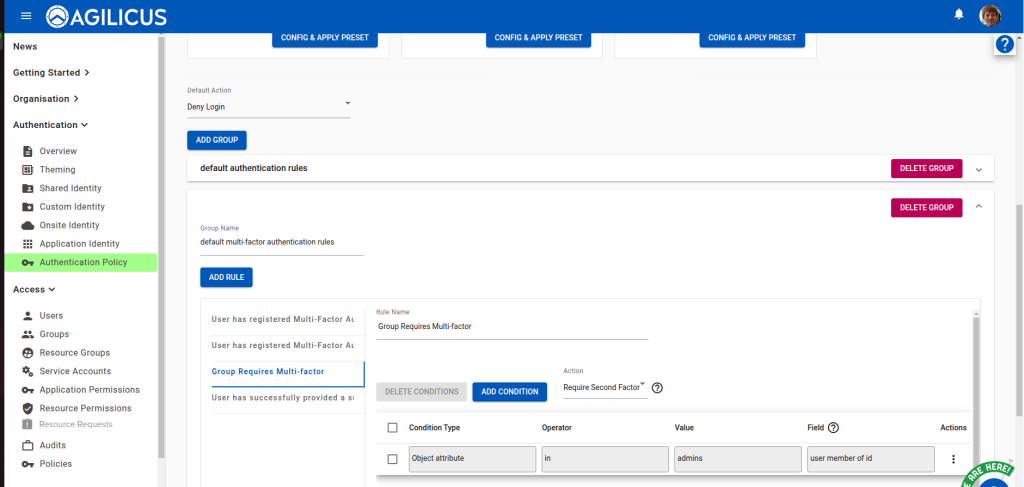
If the group you want does not exist, create it first. If you have customised the policy, you can either edit the existing rule which controls this behaviour, or create a new one. Under the “default multi-factor authentication rules” group, select the “Group Requires Multifactor” rule, then configure its condition (via the actions menu).
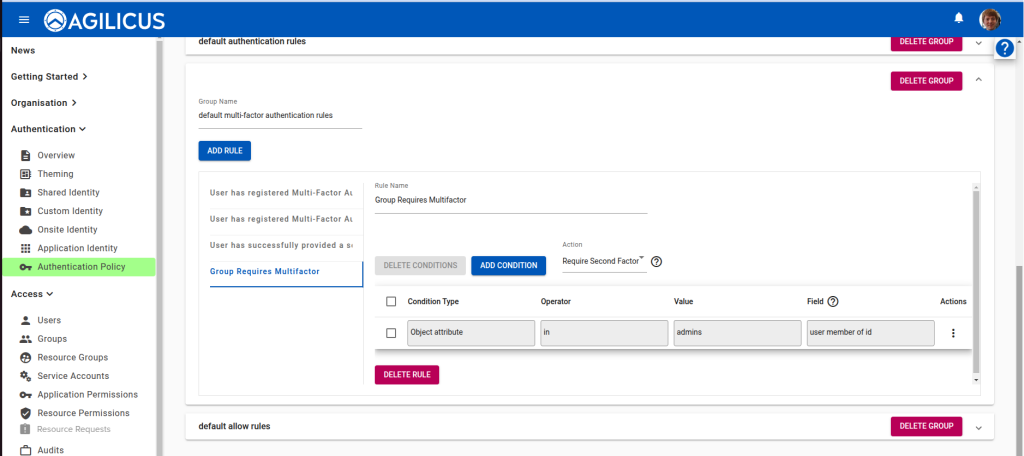
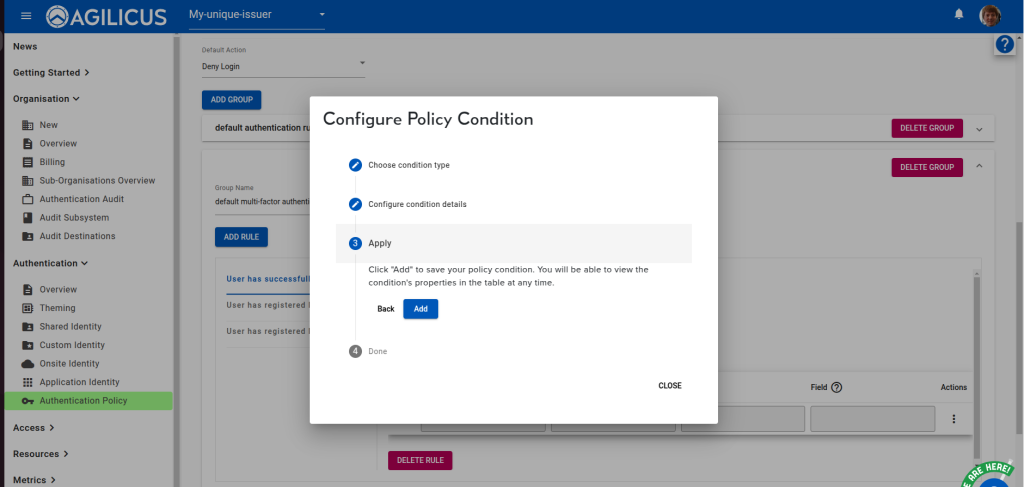
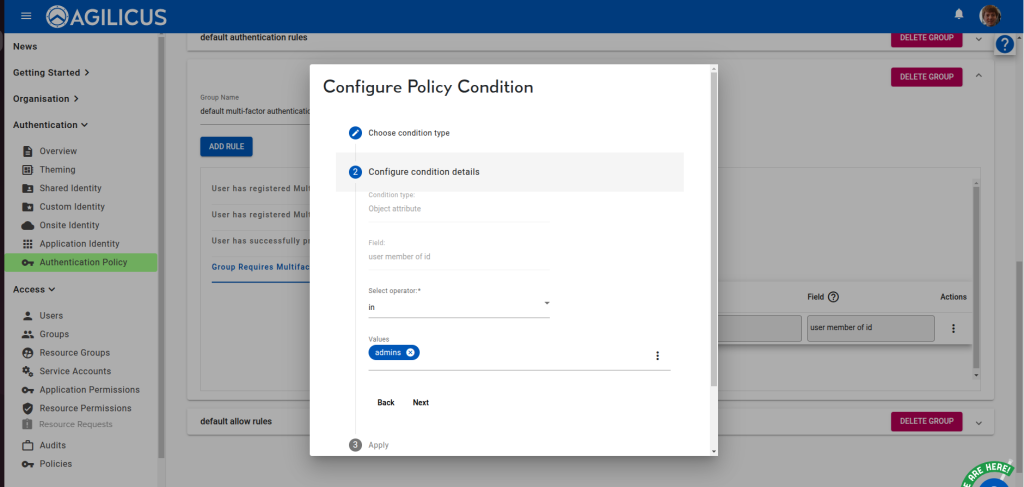
Choose “Configure condition details”, then select the desired groups in the “Values” chiplist. Do not change the operator. Once you have chosen the groups, navigate to “Apply” and click “Add”.
If this rule does not exist, you will need to create a new one in the “default multi-factor authentication rules” group. First, click “Add rule”, then select the newly created, blank rule. Change its name to “Group Requires Multi-factor”:
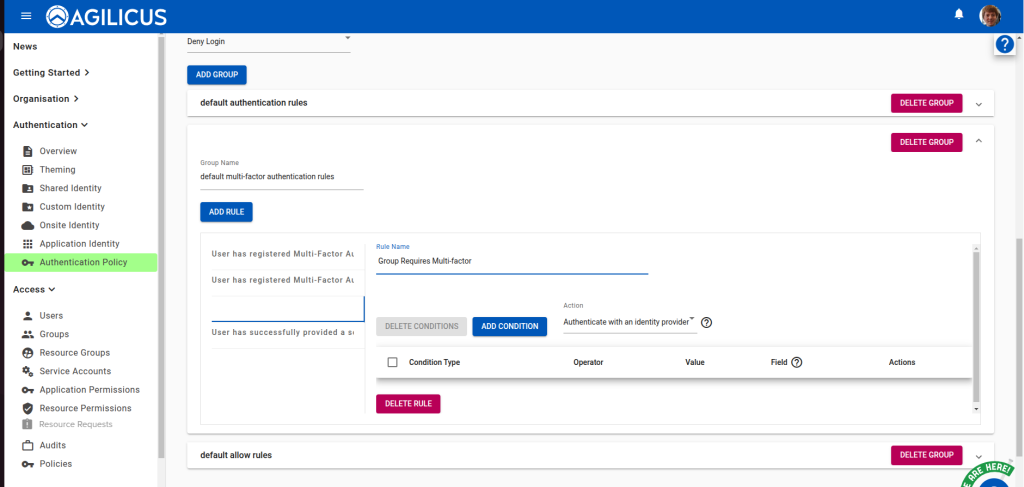
Set its Action to “Require Second Factor”.
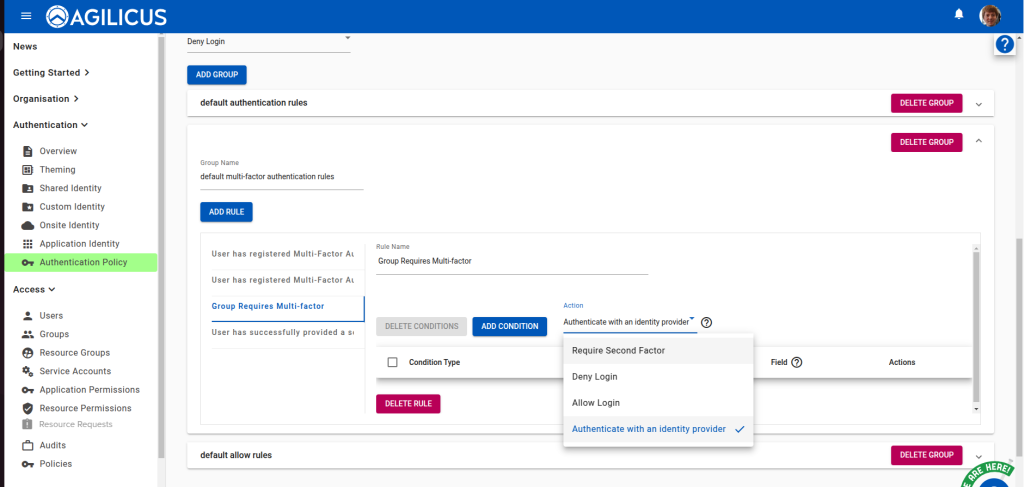
Then add a new condition. Set its type to “Object attribute” with field “user member of id.
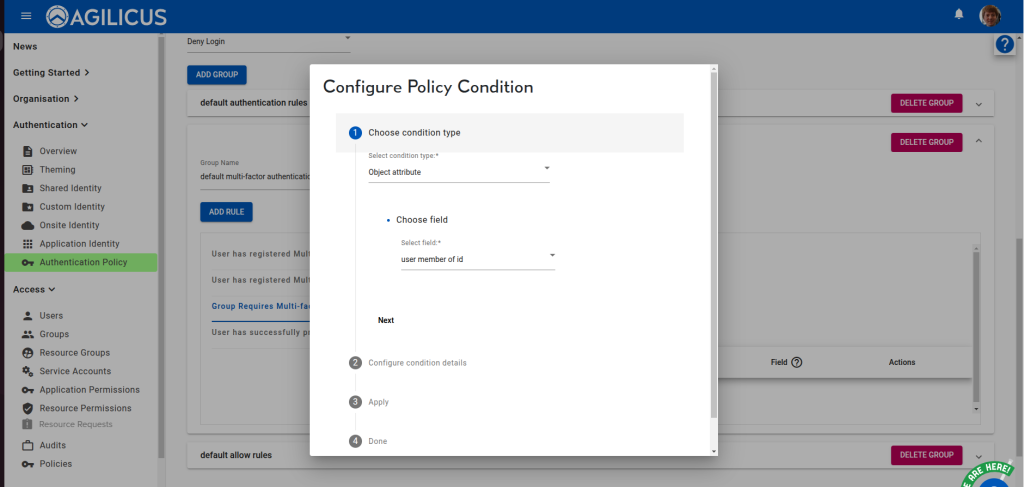
Move next to “Configure condition details”, where you will choose the “in” operator. Select the desired groups under “Values”.
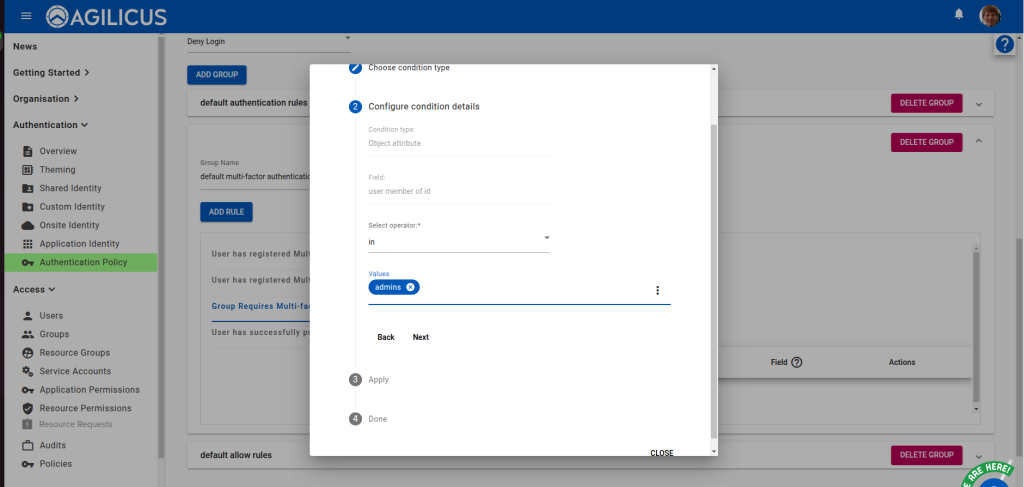
Move next to Apply to add the condition. Once you done so, the policy will be updated, and users in the configured groups will be forced to provide a second factor.
Multi-Factor Authentication Frequency
Similar to an authentication session, a user’s proof of their second factor is only valid for a configurable amount of time. This configuration is part of the authentication policy. The duration for how long the second factor is valid is expressed in seconds. It can be configured either by applying a new preset, or by editing the appropriate authentication rule.
To apply a preset, choose the desired one from the “Authentication/Authentication Policy” page, then choose the time interval.
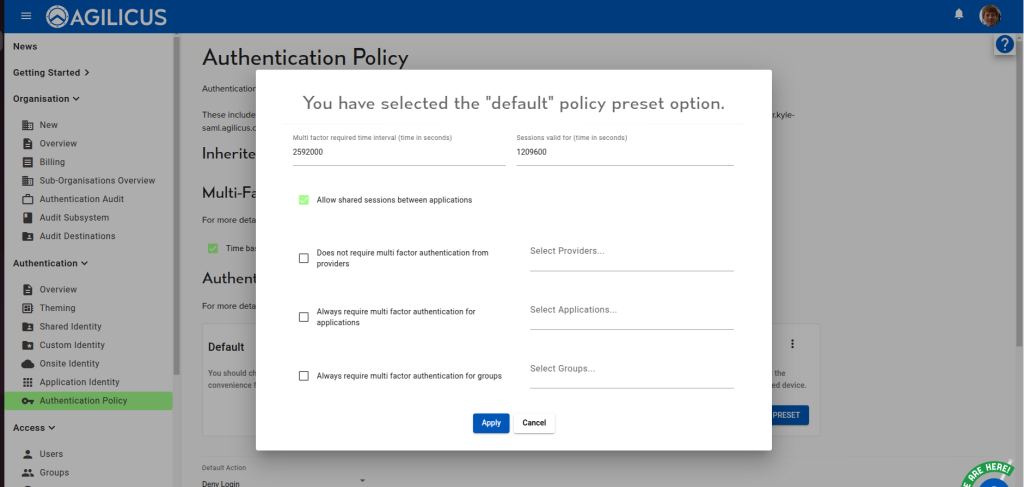
In this example, users will be asked to present their second factor every 2592000 seconds (30 days). Choose your desired value, then hit apply.
To configure the existing policy, open the “default multi-factor authentication rules” group, and choose the “User has succesfully provided a second factor within time window” rule.
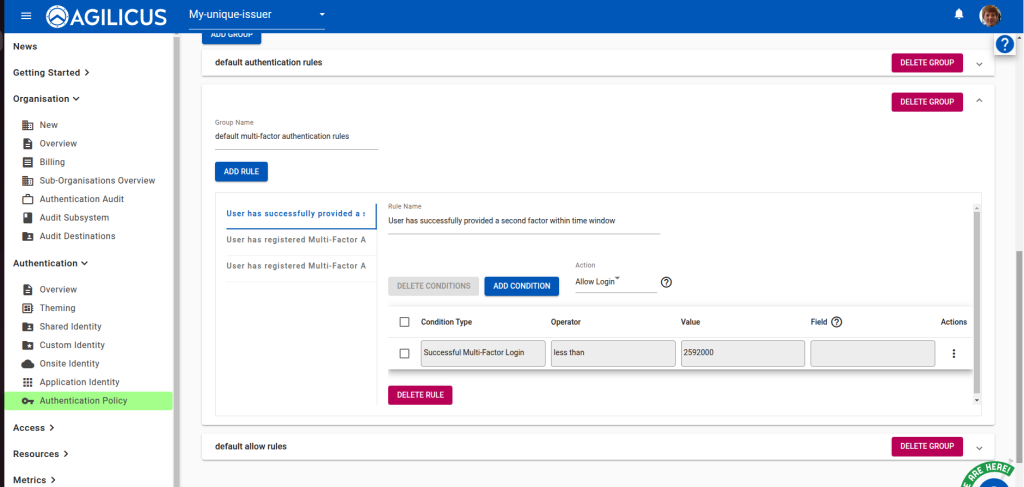
Edit the value by selecting “Configure Condition” from the actions menu.
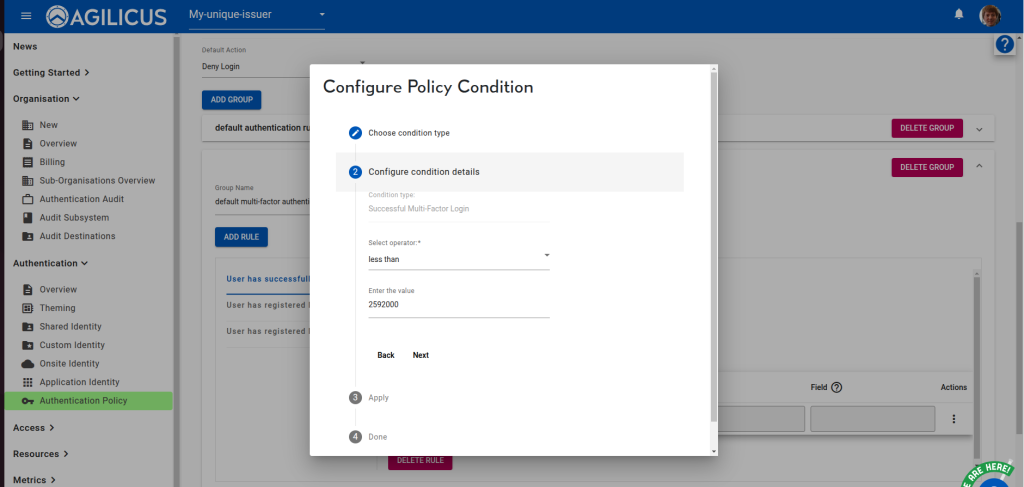
Then apply the change by select “Add”.