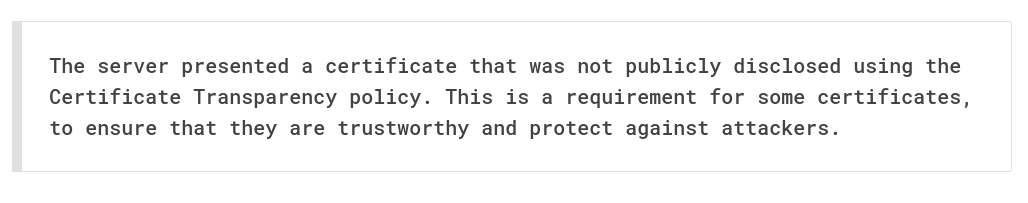
Recently a team mate ran into an issue. His browser would not let him proceed to a site he had just setup, with a valid certificate. We use Let’s Encrypt (and our sites are all in the HSTS preload so they must be TLS). Nonetheless, he was presented an error “The server presented a certificate that was not publicly disclosed using the Certificate Transparency policy. This is a requirement for some certificates, to ensure that they are trustworthy and protect against attackers.” What could be wrong?
Well in this case I asked him what time it was. He gave me an answer about 1 minutes in the past. Huh. Is your systemd-timesyncd running? No, its dead. Aha! Your NTP time is off by about 2 minutes. This certificate, from your perspective, will only become valid in the future.
We can check this using the Certificate Transparency logs. My favourite way to search them is crt.sh. This gives you a list of all Certificates issued, when, by who.
Its a good spot to check if someone is trying to spearphish your domain. Check for common mispellings.
So check your clocks. Its not enough to be close, you need to be exact. Else you might be p0wnd.