Recently there has been a DDoS attack against VoIP provider voip.ms. A tough problem to deal with for sure. And, one of the challenges relates to the end-users and the inevitable reconfiguration of their in-premise devices.
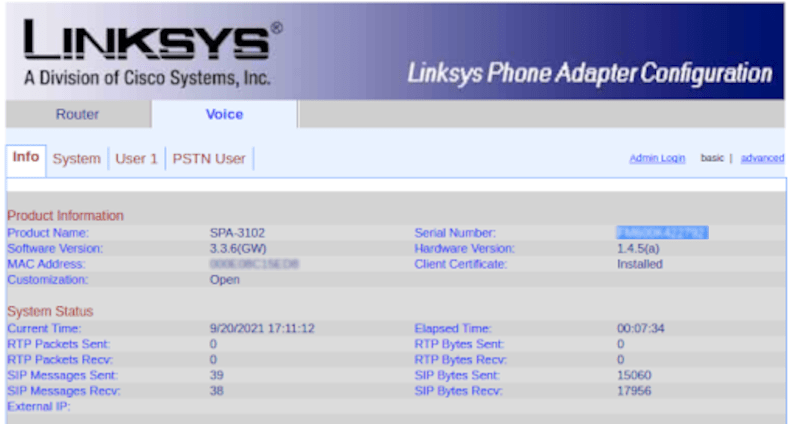
Many of the end users have devices like a Cisco SPA-3102, a > 10 years old widget. These devices have worked hard doing the same thing over and over, day in and day out. And, they have received no software updates in a long time. It would be unsafe to allow their manage console to have Internet access, or even lateral access within the network. Strong identity, multi-factor authentication, etc have passed them by.
Many of these devices are in lights-out or remote locations. What is a safe and secure way to remotely administer them so you have strong identity and an audit trail? Some would say, well, VPN to the building they are in, that is fine. But, then that means they are always accessible to all VPN users.
Others would say, get in a car and drive over. There has to be a better way. And, of course, one of our customers found one. So I thought I would share.
Ingredients:
- raspberry pi
- Cisco SPA-3102
- Frustration with voip outage
- Agilicus Identity-aware web application firewall
- A sprinkling of multi-factor authentication
So, the use case here… the Cisco device management console gets a new TLS-protected HTTPS endpoint on the public Internet. No VPN needed. And, not a single packet hits it except for an authorised user, courtesy of an identity-based proxy. Open browser from work, change the DNS name of the sip server, and boom, back to receiving telemarking duct-cleaning calls in peace. Progress!
The moral of the story. Old devices can have modern access securely, without a fuss.